.webp)
What is ISO 27001 and why is it important?
Heading 1
Heading 2
Heading 3
Heading 4
Heading 5
Heading 6
Lorem ipsum by sit amet, consectetur adipiscing elit, sed do eusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Dis aute irure door in reprehenderit in voluptate velit se cillum dolore eu fugiat nulla pariatur.
Block quote
Ordered list
- Item 1
- Item 2
- Item 3
Unordered list
- Item A
- Item B
- Item C
Bold text
Emphasis
Superscript
Subscript

Heading 1
Heading 2
Heading 3
Heading 4
Heading 5
Heading 6
Lorem ipsum by sit amet, consectetur adipiscing elit, sed do eusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Dis aute irure door in reprehenderit in voluptate velit se cillum dolore eu fugiat nulla pariatur.
Block quote
Ordered list
- Item 1
- Item 2
- Item 3
Unordered list
- Item A
- Item B
- Item C
Bold text
Emphasis
Superscript
Subscript

The core of ISO 27001
The ISO 27001 standard sets out numerous information security requirements. Certification according to this standard is therefore a powerful way to demonstrate that your organization has its information security in order. It's all about protecting the availability, integrity, and confidentiality (BIV) of information within your company. ISO 27001 provides a framework for identifying, assessing, and managing these threats. For example, carrying out a risk assessment and determining the necessary measures, such as risk mitigation or risk treatment, to prevent these problems.
How do you get to the ISO 27001 standard?
The standard is available from the Royal Netherlands Standardization Institute Foundation, or the NEN. We notice that organizations are not familiar with this standard and find learning it time-consuming. Fortunately, our consultants are familiar with the standard. They know exactly how to apply our templates, which are fully aligned with the standard, in any organization.
Why ISO 27001 certification?
In the rapidly changing digital world, organizations are constantly facing information security challenges. For example, organizations are confronted with threats to their information security every day, which means that data leaks, financial losses and image damage are increasingly common. ISO 27001 offers a solution for this and is more than a piece of paper because it offers the following benefits:
• Incident protection
Thanks to the ISO 27001 framework and management system SIMS identify your risks and implement control measures. This reduces the risk of incidents within the organization.
• Benefits in tendering
With ISO 27001, you show as an organization that the information you keep is safe. That is why it is increasingly a hard requirement when it comes to tenders. You don't have to provide an entire book showing that you're dealing well with data. By only showing the certificate, you give potential customers sufficient confidence. In addition, it gives you an advantage over your competitors who do not have a certificate.
• Customers/suppliers
ISO 27001 shows that your organization takes information security seriously. This gives trust to customers and suppliers. Large organizations increasingly expect their suppliers to be ISO 27001 certified. For example, a hospital's entire supply chain must be certified and able to demonstrate that they handle patient data correctly.
• Legislation and regulations
The standard is in line with various data protection laws and regulations, such as the AVG. Do you comply with the ISO 27001 standard? Then you don't have to worry about not complying with laws and regulations.
• Insight and control over security risks
A thorough risk assessment and risk management is required for ISO 27001 to identify potential vulnerabilities.
What components does the ISO 27001 standard consist of?
The ISO 27001 standard consists of two main parts: the Harmonized Structure (HS) and Annex A. These two parts contain different structures and contents.
PART 1
Harmonized Structure (HS)
The HS was introduced to bring consistency to all management system standards so that organizations that implement multiple standards can do so in a standardized way. The HS consists of 10 chapters:
• CHAPTER 1
Scope
Describing the scope of the standard, specifying which organizations and situations it applies to.
• CHAPTER 2
Normative references
Naming documents that are referred to and that are part of the standard. These references are necessary for understanding and applying the standard.
• CHAPTER 3
Terms and definitions
Establishing a list of terms and definitions used in the context of the standard.
• CHAPTER 4
Organization context
Identifying the relevant external and internal factors that influence
information security, such as market changes and business objectives. Here, it is important that management is involved in information security.
• CHAPTER 5
Leadership
Demonstrating management commitment. Such as naming a Security Officer to take the lead in the information security policy and associated strategy.
• CHAPTER 6
planning
Preparing an annual information security plan that includes priorities and objectives. In addition, identify the important issues and risks that need to be addressed.
• CHAPTER 7
Support
Allocating resources and training to employees for information security awareness and training.
• CHAPTER 8
Outturn
Implementing, organizing and controlling technical measures, such as firewalls and encryption, to protect information.
• CHAPTER 9
Performance evaluation
Periodically assessing incidents and audits to measure the effectiveness of information security measures.
• CHAPTER 10
Improvement
Treating and dealing with anomalies, including responses, corrective actions and evaluation of causes. The documentation of anomalies and the assessment of corrective actions are important.
PART 2
Annex A
The Annex A to ISO 27001 contains a list of control measures and controls that organizations can implement to mitigate risks. These control measures are divided into different categories:
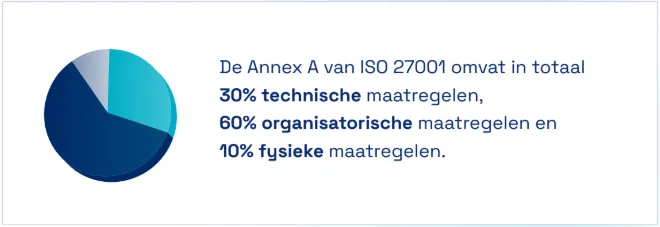
A5: Organizational control measures
This chapter contains control measures that relate to the organizational structure and how information security is controlled within the organization. These measures include:
• Assignment of responsibilities;
• Determining acceptable use of assets;
• Setting up a password policy;
• Promoting a “Clean Desk and Screen Culture”;
• Setting up plans and procedures to ensure the continuity of business activities, even in the event of emergencies or emergencies;
• Managing and protecting assets (infrastructure, network, systems and other assets);
• Developing and maintaining clear communication channels and business processes;
• Complying with regulations (GDPR, European legislation).
A6: People-centered control measures
Here, everything revolves around the human aspect of information security. The control measures in this chapter focus on the behavior and actions of employees. Think about:
• Establishing rules and procedures for staff;
• Managing risks related to human error, theft, fraud, and abuse;
• Implementing recruitment and exit screening processes.
A7: Physical controls
This chapter covers physical security measures aimed at protecting the organization's physical infrastructure.
This includes measures such as:
• Access control to buildings and spaces;
• Cabling security;
• Protection of mobile devices (such as laptops outside the home);
• Fire protection.
A8: Technological control measures
Here, everything is focused on the technological field of information security. The control measures in this chapter focus on systems, capacity and software.
Think about:
• System and software development and maintenance (documentation, processes);
• Backup policy;
• Protection against viruses;
• Maintaining servers and PCs;
• Rights Management.
Continuous improvement in ISO 27001
During an ISO 27001 audit, the auditor will always follow the PDCA (Plan Do Check Act) cycle in his assessment. They check whether the plans were effective (Plan), whether the execution was carried out correctly (Do), whether controls were carried out (Check) and whether appropriate adjustments were made (Act). Auditors will look for evidence of cycle effectiveness and management's willingness to adapt and improve. It's all about ensuring a constant process of learning, adapting and growing.
Plan
In the first phase of continuous improvement (Plan), the organization looks at where improvement is needed and sets goals for information security. This includes:
• Evaluating the results of risk assessments and ISO audits to identify weaknesses and deficiencies;
• Setting measurable information security objectives;
• Developing action plans and assigning responsibilities for achieving these goals.
Do
After planning, the implementation phase (Do) follows, in which the action plans are implemented. This includes:
• Implementing the planned security measures and actions;
• Training and making employees aware of the new
measures;
• Collection of data and information during deployment
Check
In the control phase (Check), it is evaluated whether the measures taken are effective in improving information security. This includes:
• Monitoring and measuring performance and security indicators;
• Comparing results with established objectives and standards;
• Identify anomalies and areas that require further improvement.
Act
Based on the findings in the control phase (Check), corrective and preventive measures are taken in the final phase (Act). This includes:
• Implementing corrective actions to address identified
addressing anomalies;
• Identifying causes of problems and preventing
repetition;
• Documenting the measures taken and the results of the
improvement efforts.
The effect of the PCDA model
The PDCA model creates a feedback loop that enables organizations to continuously learn and evaluate their approach to information security. By repeating this process regularly, organizations can maintain and improve their security levels in an ever-changing threat environment. Continuous improvement within ISO 27001 is not only an obligation under the standard, but also an opportunity for organizations to become more effective in protecting their sensitive information and meeting stakeholder expectations. It is not without reason that a management system must run for at least three months before your organization can be certified.
The difference between ISO 27001 and ISO 27002
The difference between ISO 27001 and ISO 27002 lies mainly in the level of detail at which the control measures are written out. Another important difference between these two standards is that you can certify for the 27001 and not for ISO 27002. Indeed, ISO 27002 was developed to provide organizations with guidelines and best practices for information security. It is therefore an additional standard that goes deeper into ISO 27001.
ISO 27002 contains a list of possible control measures, also known as “controls”. These controls are specifically designed so that they can be implemented using ISO 27001. Indeed, the controls are in line with the measures in Annex A of the ISO 27001 standard.
In short, ISO 27002 provides guidelines and best practices for information security, while ISO 27001 focuses on setting up, implementing, maintaining, and improving an ISMS (Information Security Management System).
ISO 27001 Awareness
The ISO 27001 standard highlights the importance of awareness and refers to understanding and acknowledging the importance of information security within an organization. It's not just about understanding the existing security measures, but also about realizing the potential risks and the role that employees play in ensuring information security.
Often, the main challenge is to create sufficient awareness. 80% of cyber incidents are caused by inattention or wrong behavior on the part of employees. That is why it is crucial that your employees are aware of the risks. Additional awareness training is not only a mandatory part of the standard (according to A.6.3), but also ensures that everyone actually follows the necessary agreements and rules of conduct.
How to implement ISO 27001
Before you get started with an ISO certification, you'll need to know how to implement it. Implementing ISO 27001 is a process that helps organizations establish, implement, manage, and improve their Information Security Management System (ISMS).
An implementation process that suits your organization
Our customers choose from various implementation processes that suit the wishes and needs of the organization. Read here the white paper about what our implementation process looks like, what method we use and the differences between our customized implementation processes. We hope this blog has provided you with a clear insight into what the ISO 27001 standard entails.
Want to know more about the standards in this article?
More information is available on our website: fendix.nl/standards
Are you enthusiastic about our approach and looking for an ISO specialist or ISO professional?
Then we would love to hear from you. Contact us below for an informal, free consultation.


.png)